Why Should You Consider Application Security Automation?
Audacix
JANUARY 31, 2024
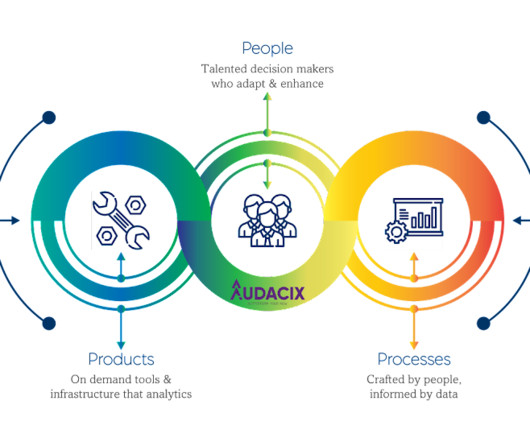
Table Of Contents As NIST recommends organizations make the most of technology to shape and craft their own cybersecurity strategies with its Cybersecurity Framework (CSF) 2.0 , all the leading and emerging businesses in some of the world's critical infrastructure like the banking and energy industries must consider application security automation.





























Let's personalize your content